Live Frida session
A persistent Python agent stays attached to the target process over the entire engagement. Install hooks, drain events, re-query — state survives between UI actions instead of re-spawning a fresh session per call.
Android + iOS · OWASP MASTG v1.7 aligned
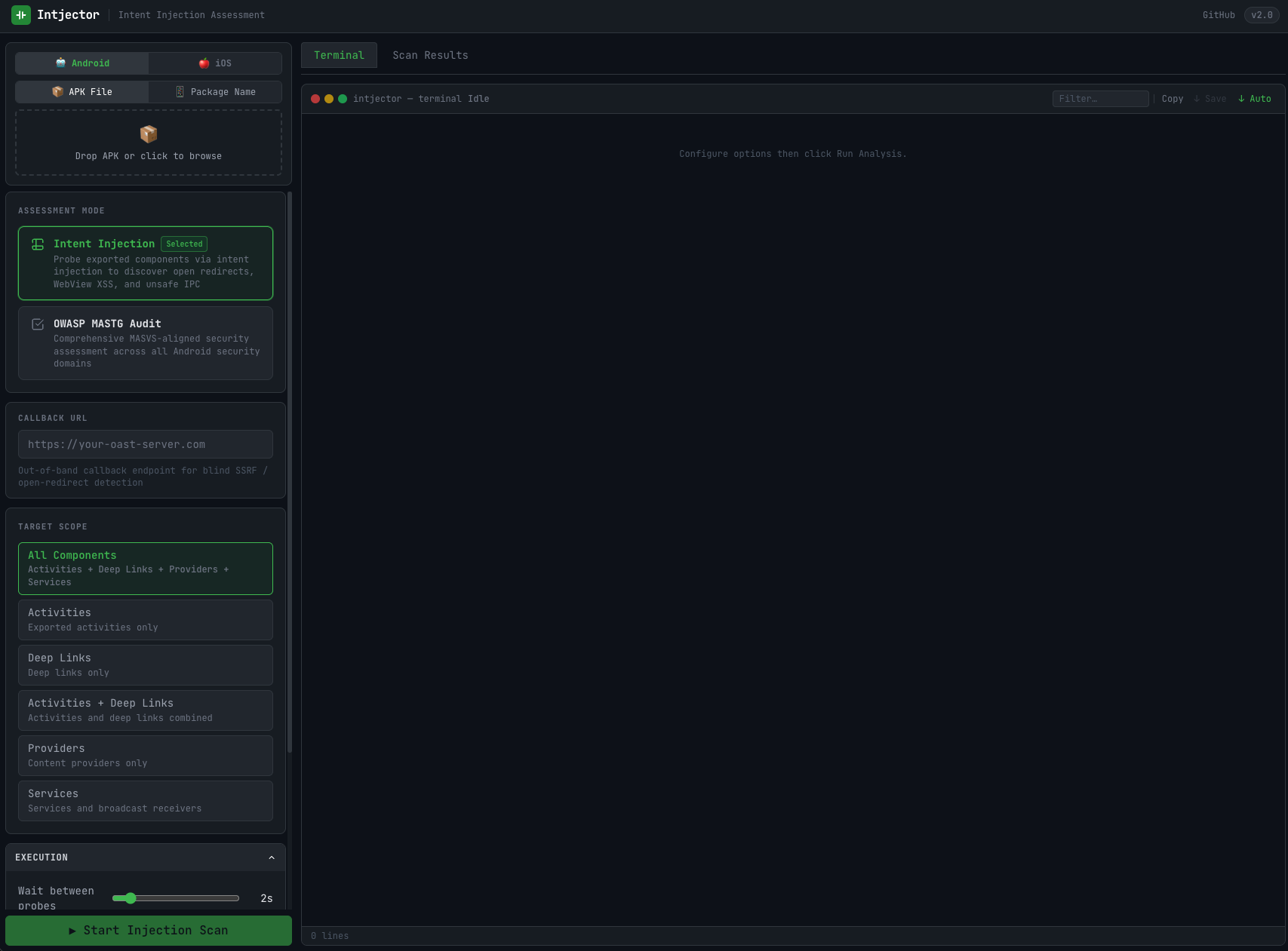
intjector is a one-click security scanner for Android APKs and iOS IPAs. Static analysis plus an embedded Frida runtime — deep-link fuzzing, keychain & keystore dumps, SSL pinning bypass, WebView bridge taps — all driven from a browser UI.
Two engines — static and dynamic — covering both platforms, mapped directly to MASTG categories.
android:debuggable, networkSecurityConfig.parseUri / intent-redirect, App Links (assetlinks.json) verification.setJavaScriptEnabled, @JavascriptInterface bridges, file-access flags, mixed content.grantUriPermissions, path-traversal sinks..mobileprovision & certs.continueUserActivity:, OAuth redirect hijack..appex) — privileged extension points, TRUEPREDICATE activation, full-access keyboards.A persistent Python agent stays attached to the target process over the entire engagement. Install hooks, drain events, re-query — state survives between UI actions instead of re-spawning a fresh session per call.
iOS: dump every keychain item the process can see (GenericPassword, InternetPassword, Certificate, Key, Identity) with full attribute dict. Android: walk SharedPreferences, EncryptedSharedPreferences, SQLite DBs, Keystore aliases.
Navigate the sandbox from the browser: bundle, Documents, Library, Caches, Preferences, tmp. Inline preview for any file under 4 MB — UTF-8 auto-decode falls back to base64 for binaries. File protection class shown per entry.
Enumerate NSHTTPCookieStorage (name, value, domain, path, flags) and NSUserDefaults.dictionaryRepresentation. Android counterpart dumps every SharedPreferences file under the data dir.
List every ObjC or Java class, filter by name, and click through to see its methods. Useful for finding auth wrappers, crypto helpers, and jailbreak checks in obfuscated code — without opening a terminal.
Send any myapp:// URL or Android intent to the running app from the UI. The scheme fuzzer tries nine built-in payloads — empty URL, open redirect, javascript:, path traversal, null-byte — to find deep-link handlers that don't validate input.
One click installs hooks on SSL_set_verify (BoringSSL), SecTrustEvaluate / SecTrustEvaluateWithError, AFSecurityPolicy (AFNetworking), and TSKPinningValidator (TrustKit). Lets you intercept HTTPS traffic without modifying the app binary.
Disables OkHttp CertificatePinner, Conscrypt, X509TrustManager, WebViewClient.onReceivedSslError, and Network Security Config pin sets in one step. Works even when an app uses several TLS libraries at once.
Hides jailbreak and root indicators from the app. On iOS, hooks NSFileManager.fileExistsAtPath:, UIApplication.canOpenURL:, and the libc calls stat, lstat, access, fopen. On Android, hides Magisk, superuser apps, su binaries, and test-keys.
Logs every URL the app opens or receives. Hooks UIApplication.openURL:options:, every application:openURL:options: implementation, the legacy sourceApplication:annotation:, and continueUserActivity: — so you see every deep-link entry point, the URL, and which app triggered it.
Captures every userContentController:didReceiveScriptMessage: call with handler name, body (truncated), frameInfo.request.URL and isMainFrame. Android equivalent hooks @JavascriptInterface methods and evaluateJavascript callbacks.
Instruments NSKeyedUnarchiver legacy + secure decode, NSCoder, NSXMLParser, PropertyListSerialization. Android version hooks Parcel, Intent.getParcelableExtra, ObjectInputStream. Catch unsafe class-graph reads the moment they fire.
Uses ObjC.choose to find every WKWebView currently in memory. Shows the current URL, javaScriptEnabled, hasOnlySecureContent, number of script handlers, and inline-media flag — no need to reload the page.
Unzips an IPA, copies FridaGadget.dylib into Frameworks/, injects an LC_LOAD_DYLIB command via insert_dylib --strip-codesig, removes _CodeSignature/ + embedded.mobileprovision, repacks. Re-sign with your cert and install — no jailbreak, no dev-team source.
Lists USB / network Frida devices, enumerates installed apps with bundle-id, name, PID. Filter, click, attach — the UI handles process spawning, script loading and teardown.
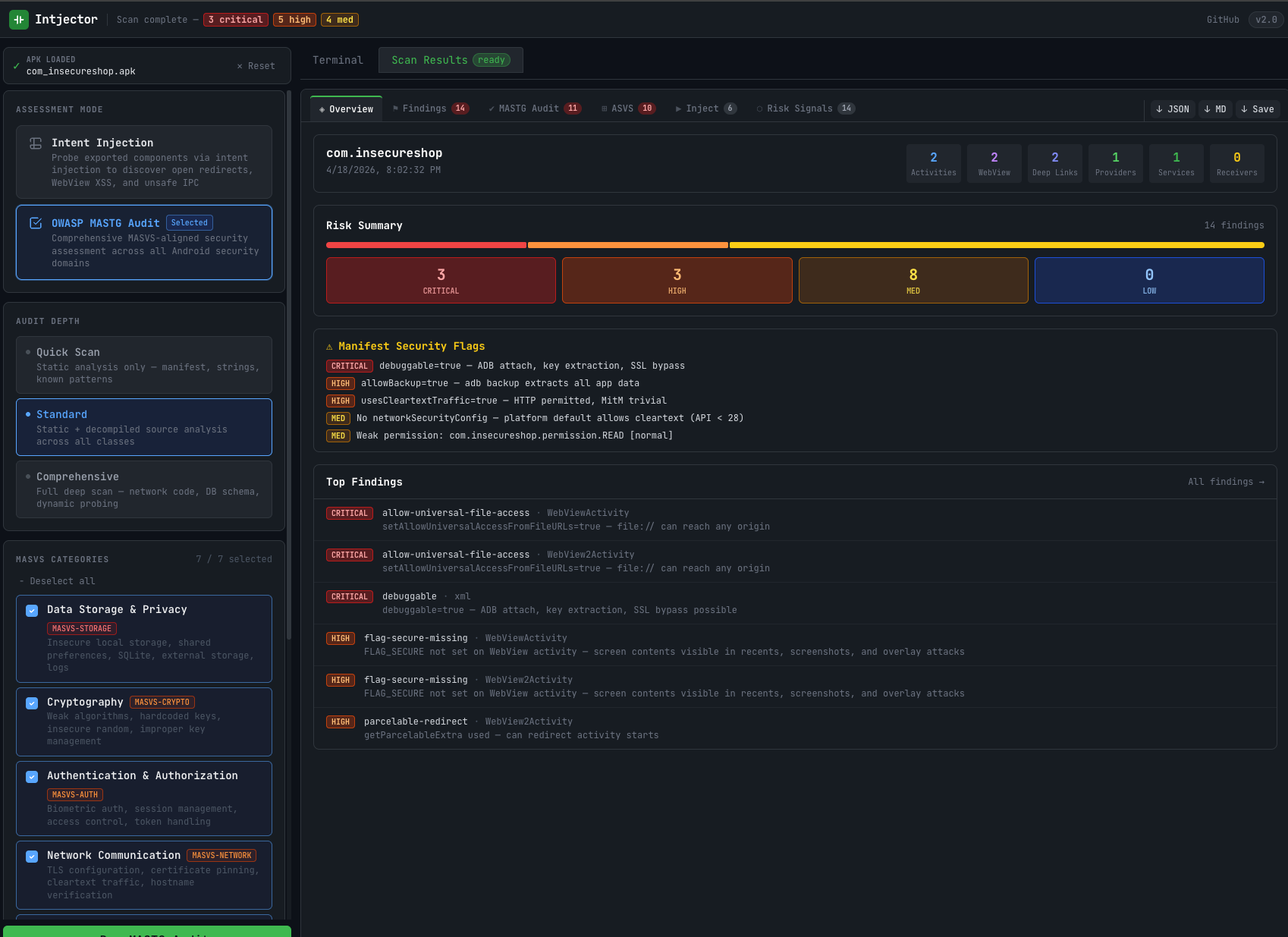
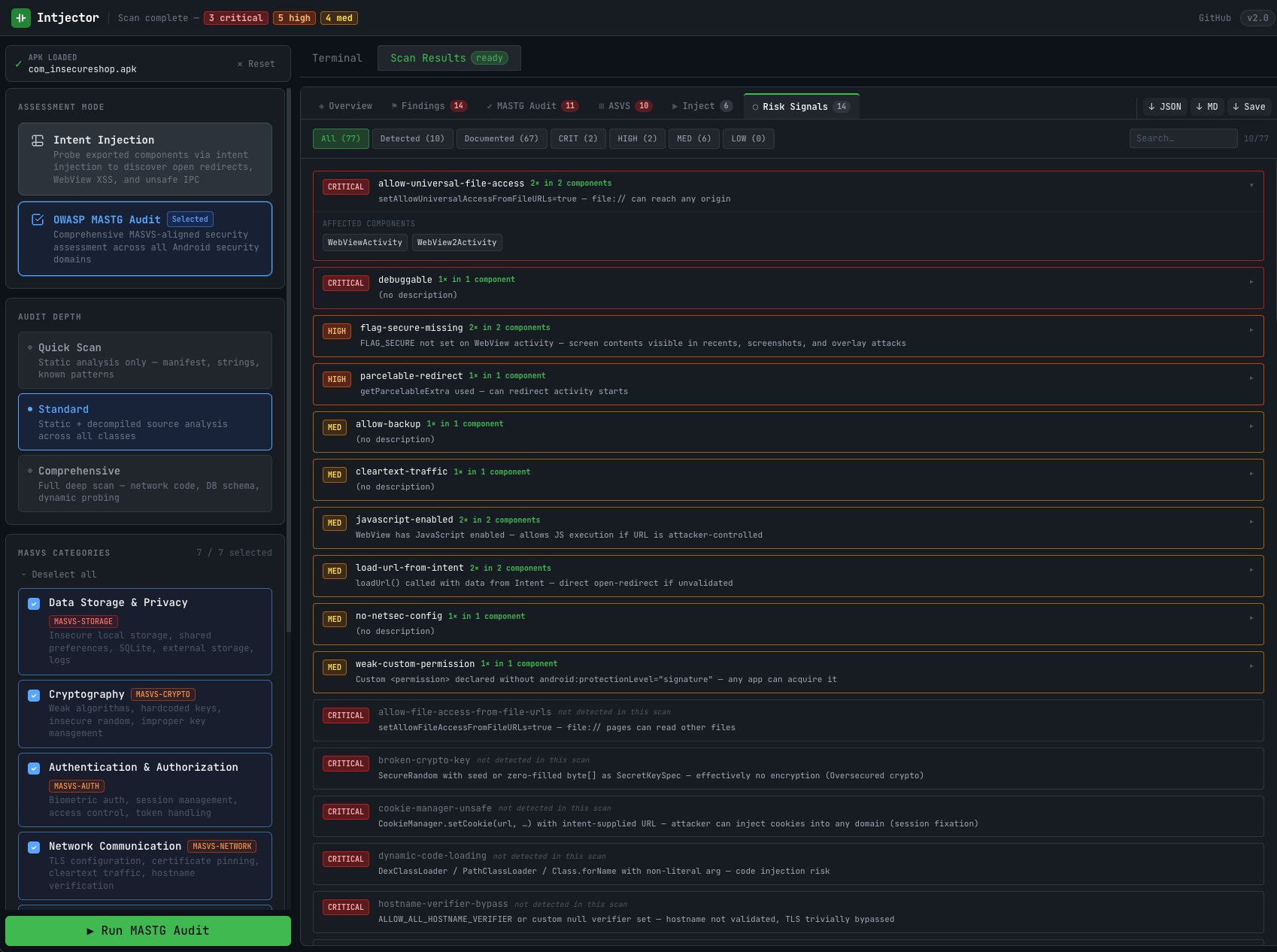
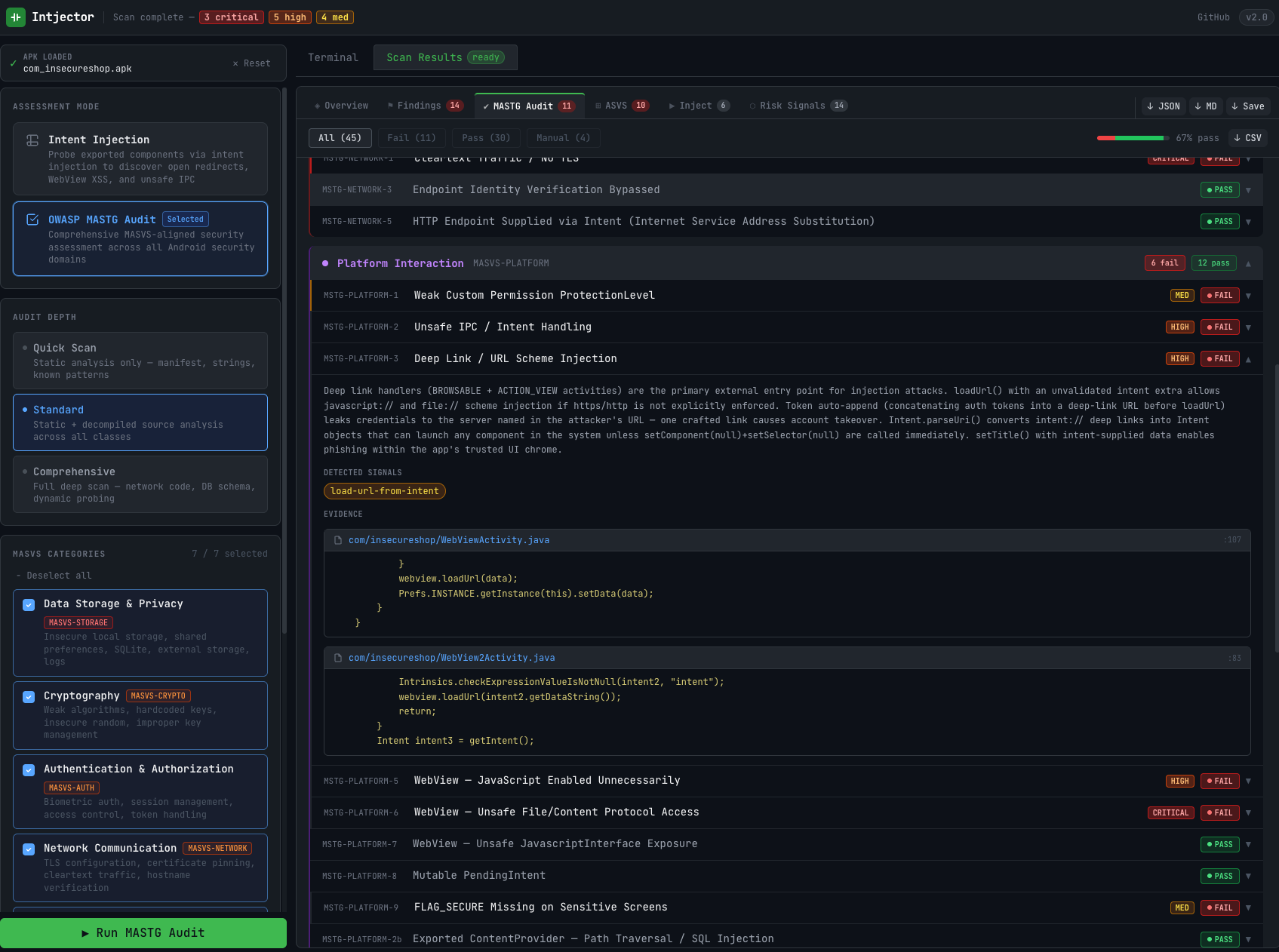
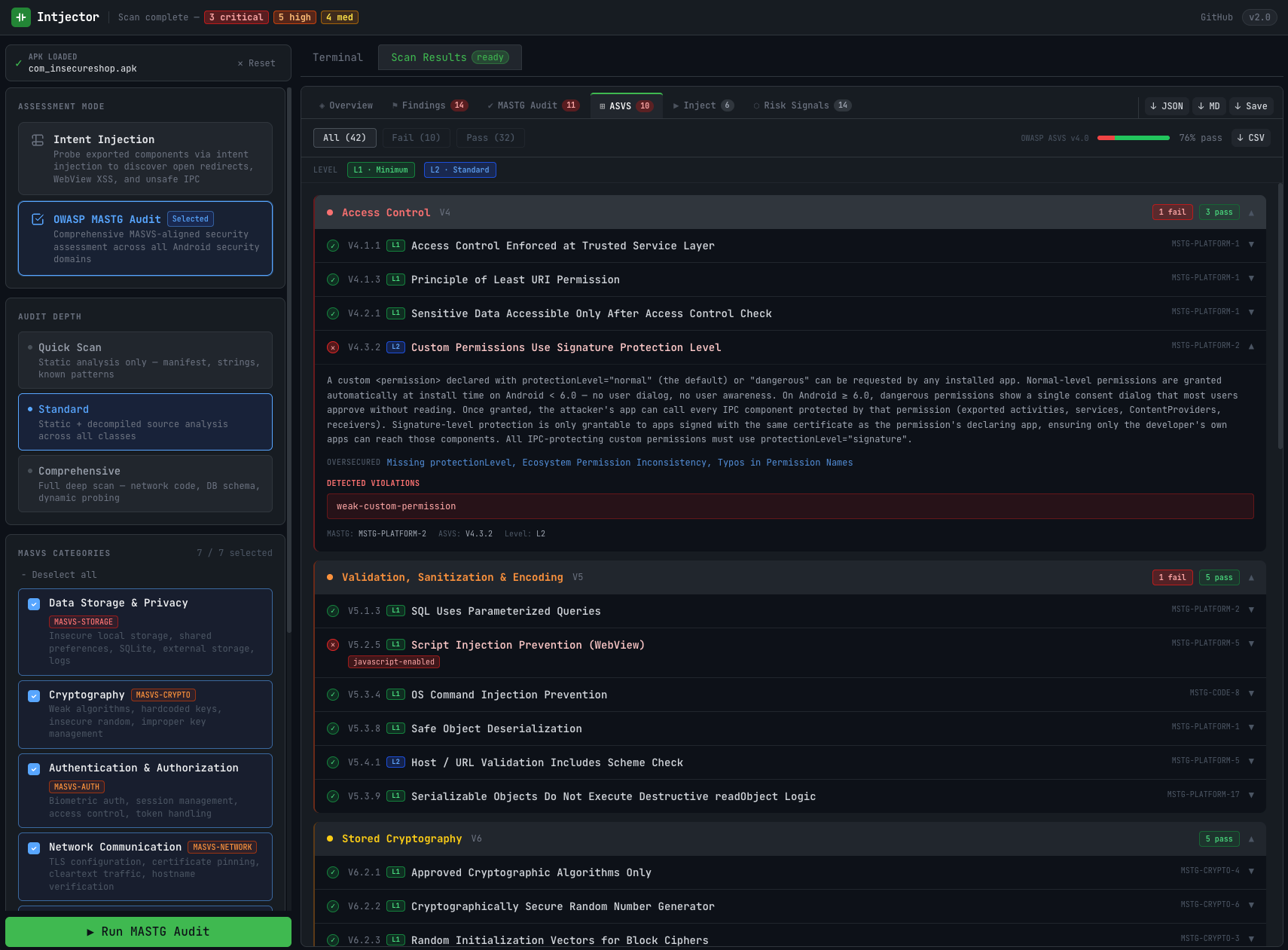
Every finding tagged CRITICAL / HIGH / MEDIUM / LOW, filterable by severity + search, mapped to MASTG test IDs. A "detected vs documented" toggle shows which MASTG checks actually fired on this build versus which are just part of the catalog.
Each signal links to a specific MASTG test case (MSTG-STORAGE-*, MSTG-CRYPTO-*, MSTG-NETWORK-*, MSTG-PLATFORM-*, MSTG-CODE-*, MSTG-RESILIENCE-*). The output can be used directly in a pentest report.
Export findings as JSON for automation, Markdown for GitHub / Notion, or Excel (.xlsx) for client delivery. The Excel export includes a dedicated MASTG and MASVS checklist sheet with pass / fail / not-applicable status per requirement.
Everything runs in a single web UI: upload, scan, attach, patch, report. No terminal, no Frida CLI setup, no Python environment to configure. Share the URL with your team — sessions persist across users.
Useful for anyone working with mobile app security.
A look at the tool in action.
intjector is in private beta. A public build is on the way.