Two engines — static and dynamic — covering both platforms, mapped directly to MASTG categories.
Live Frida session
A persistent Python agent stays attached over the entire engagement. Install hooks, drain events, re-query — state survives between UI actions instead of re-spawning a fresh session per call. Active jobs panel lists every live hook / override / monitor / bypass in one place; one click to kill any of them.
Secret stores
Android — walk SharedPreferences, EncryptedSharedPreferences, SQLite databases, and Keystore aliases.
iOS — dump every keychain item the process can see (GenericPassword, InternetPassword, Certificate, Key, Identity) with the full attribute dictionary.
Sandbox filesystem browser
Navigate the app sandbox from the browser. Inline preview for any file under 4 MB with UTF-8 auto-decode.
Android — /data/data/<pkg>/, files, databases, caches, shared_prefs.
iOS — bundle, Documents, Library, Caches, Preferences, tmp.
Cookies & preferences
Android — dump every SharedPreferences XML under the data directory plus WebView cookie store.
iOS — enumerate NSHTTPCookieStorage (name, value, domain, path, flags) and NSUserDefaults.dictionaryRepresentation.
Class / method probe + set return value
List every ObjC or Java class, filter by name, click through to see its methods. Inline set return value editor on every method — force true / false / 0 / 1 / null / any literal without writing a Frida script. Type-aware coercion handles boolean, int, long, String. Neutralise isJailbroken / isRooted / isDebuggerConnected in one click.
Pattern watch
Wildcard hook against thousands of methods at once. Type *Login*!*auth* (Android) or *[*Login* *isLoggedIn] (iOS) and a tracing hook installs on every match. Args + return values stream into the live event timeline; one install becomes one job, kill restores all hooks atomically.
Heap explorer
Grab live instances of any class with Java.choose / ObjC.chooseSync. Walk fields, call zero-arg methods on the exact object in memory. Find the live LoginManager and dump its userToken; spot every WKWebView with javaScriptEnabled = true; read decoded NSURLCredentials from the heap.
URL launcher & scheme fuzzer
Send any myapp:// URL or Android intent to the running app from the UI. The scheme fuzzer tries nine built-in payloads — empty URL, open redirect, javascript:, path traversal, null-byte — to find deep-link handlers that don't validate input.
Android TLS bypass
Disables OkHttp CertificatePinner, Conscrypt, X509TrustManager, WebViewClient.onReceivedSslError, and Network Security Config pin sets in one step. Works even when an app uses several TLS libraries at once.
iOS SSL pinning bypass
One click installs hooks on SSL_set_verify (BoringSSL), SecTrustEvaluate / SecTrustEvaluateWithError, AFSecurityPolicy (AFNetworking), and TSKPinningValidator (TrustKit). Lets you intercept HTTPS traffic without modifying the app binary.
Root / jailbreak / biometrics bypass
Hides root and jailbreak indicators, and forces biometric checks to succeed.
Android — hides Magisk, superuser apps, su binaries, and test-keys; strips FLAG_SECURE from windows so screenshots work for evidence; observes KeyStore.load / getKey / aliases usage.
iOS — hooks NSFileManager.fileExistsAtPath:, UIApplication.canOpenURL:, libc stat / lstat / access / fopen; replaces the reply block on LAContext.evaluatePolicy:reply: to force Touch ID / Face ID success.
Custom bypass-script generator
Reads your static-scan findings + SBOM and generates a Frida script that hooks only what this app actually uses — custom TrustManager and HostnameVerifier classes the scanner caught, app-specific su / magisk paths from bytecode strings, RootBeer if bundled, AFNetworking / TrustKit / OkHttp blocks conditional on imports. Smaller, faster, fewer false hooks. Saves to the codeshare library so the next scan of the same target opens with the right bypass.
Intent / openURL monitor
Logs every URL or IPC the app fires or receives.
Android — hooks Activity.startActivity*, Context.startActivity / startService / sendBroadcast, and BroadcastReceiver.onReceive; decomposes each Intent into action / data / extras / flags / categories / component.
iOS — hooks UIApplication.openURL:, openURL:options:completionHandler:, canOpenURL:, every application:openURL:options:, legacy sourceApplication:annotation:, and continueUserActivity:.
Crypto monitor
Captures every symmetric crypto / KDF / RNG call the app makes — keys, IVs, plaintext, PBKDF rounds — with hex previews streaming into the live event timeline.
Android — hooks Cipher.init / Cipher.doFinal, Mac.doFinal, MessageDigest.digest, KeyGenerator.generateKey.
iOS — hooks CCCrypt, CCCryptorCreate, CCKeyDerivationPBKDF, SecRandomCopyBytes with full argument decoding.
WebView bridge tap
Captures every message passed from JavaScript to native.
Android — hooks @JavascriptInterface methods and evaluateJavascript callbacks.
iOS — captures userContentController:didReceiveScriptMessage: with handler name, body, frameInfo.request.URL, and isMainFrame.
Deserialization tap
Catches unsafe class-graph reads as they fire.
Android — hooks Parcel, Intent.getParcelableExtra, ObjectInputStream.
iOS — instruments NSKeyedUnarchiver legacy + secure decode, NSCoder, NSXMLParser, PropertyListSerialization.
Device & app picker
Lists every USB / network Frida device (Android & iOS) and enumerates installed apps with package / bundle-id, name, and PID. Filter, click, attach — the UI handles process spawning, script loading, and teardown.
APK repackaging
Works against any debuggable build out of the box; for release APKs, re-signs with a debug cert or injects Frida Gadget into lib/<abi>/ and aligns / signs the output so it installs on a non-rooted device.
IPA patcher (no jailbreak)
Unzips an IPA, copies FridaGadget.dylib into Frameworks/, injects an LC_LOAD_DYLIB command via insert_dylib --strip-codesig, removes _CodeSignature/ and embedded.mobileprovision, and repacks. Re-sign with your cert and install — no jailbreak required.
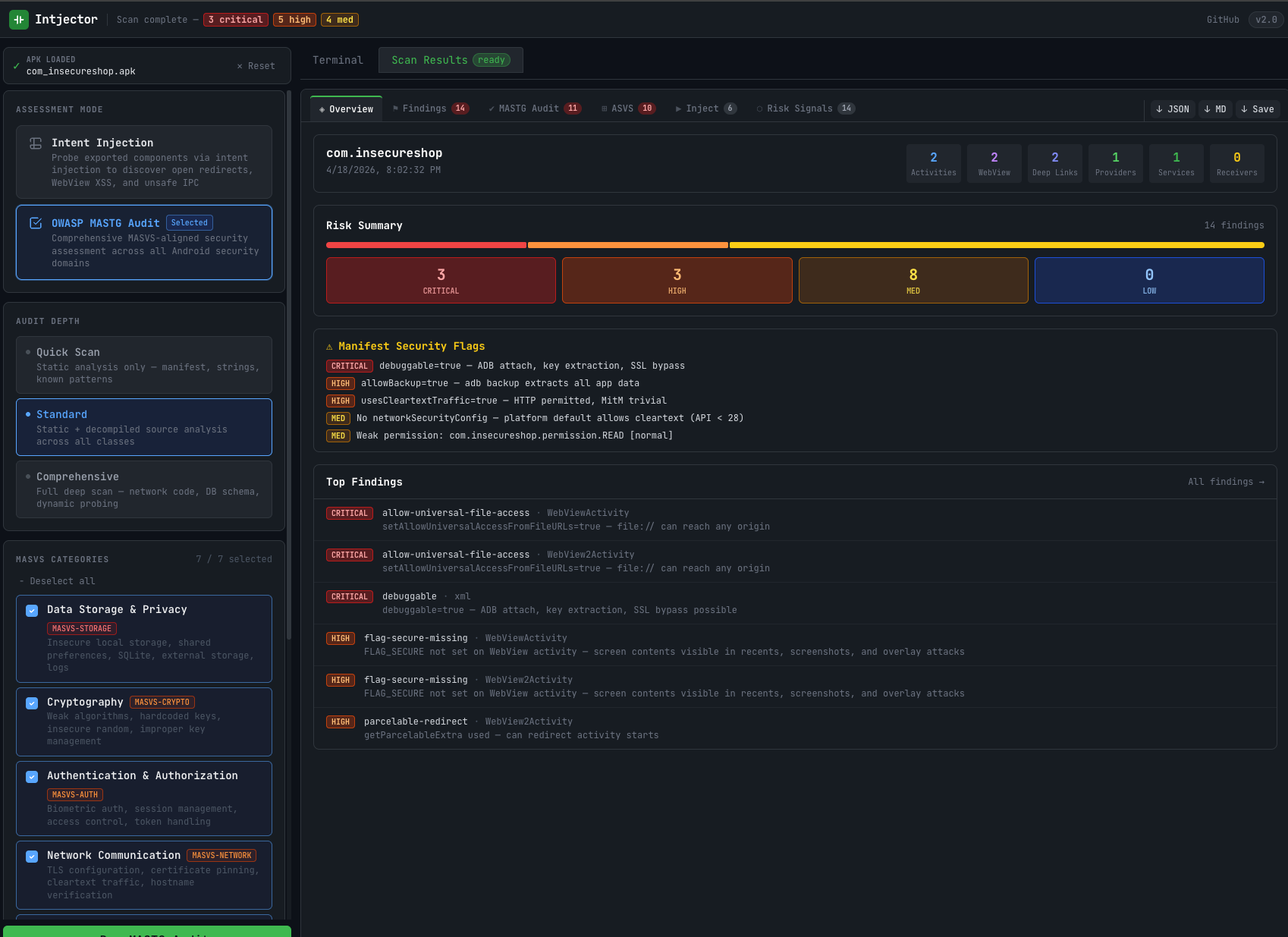
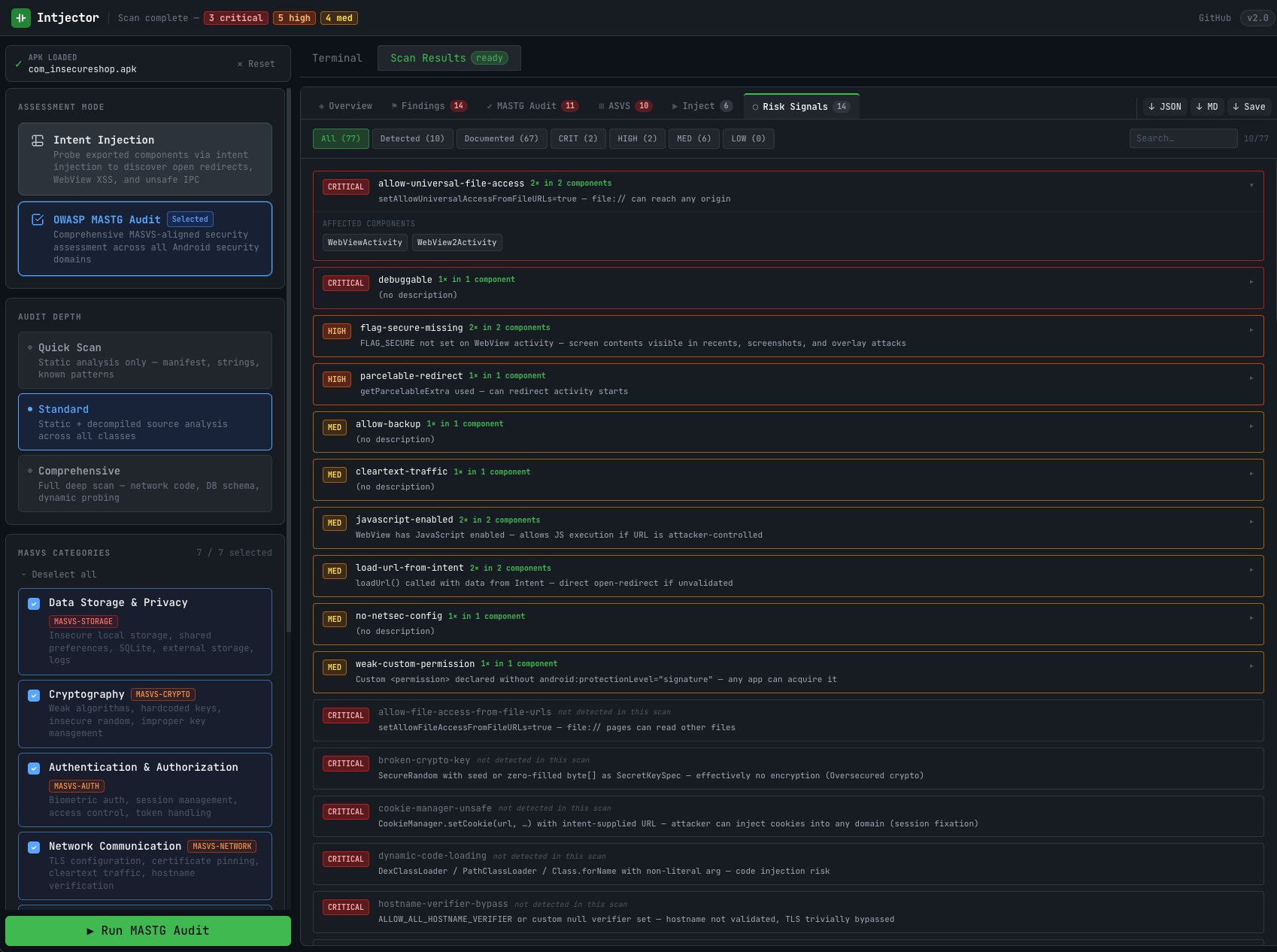
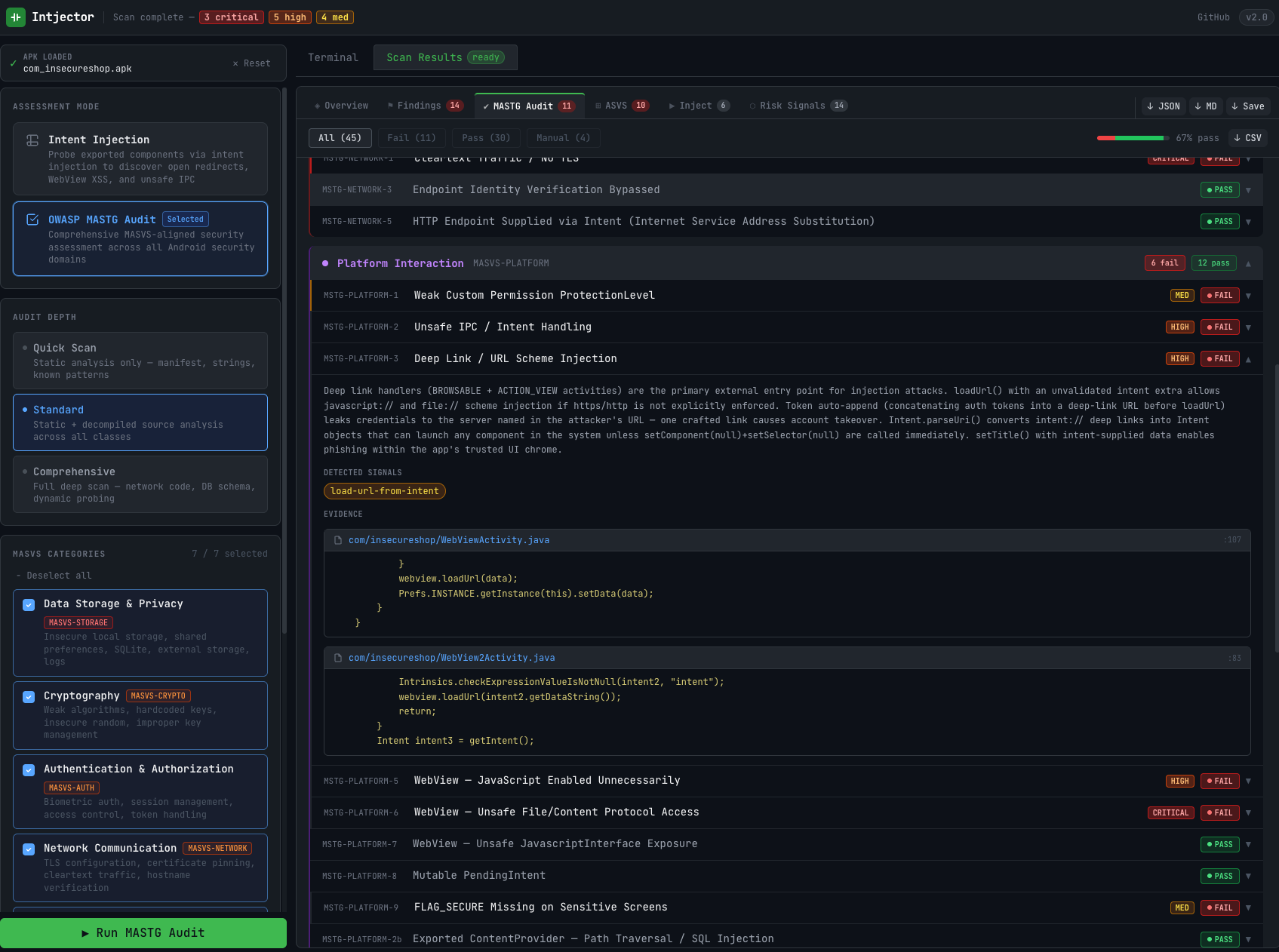
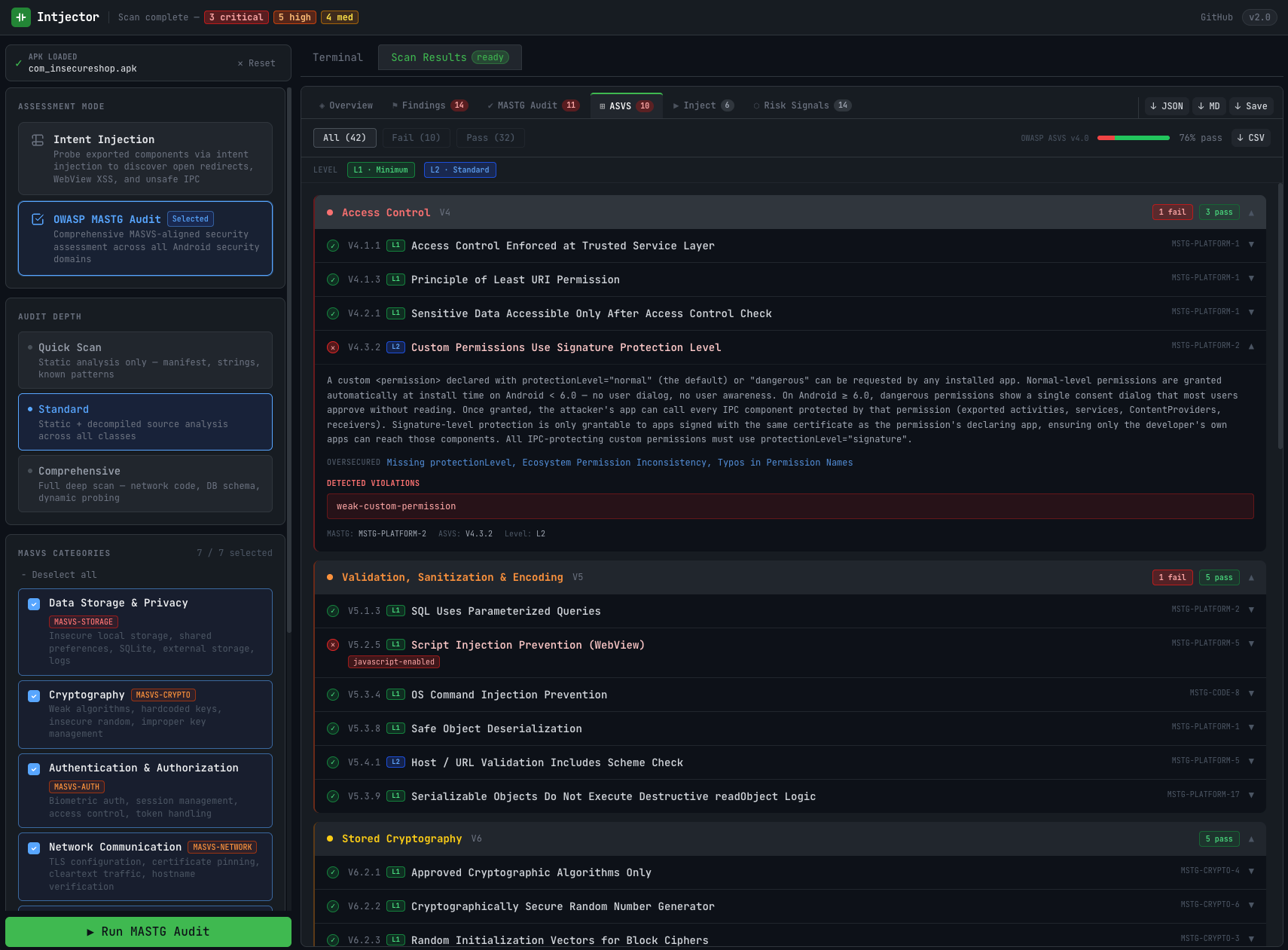
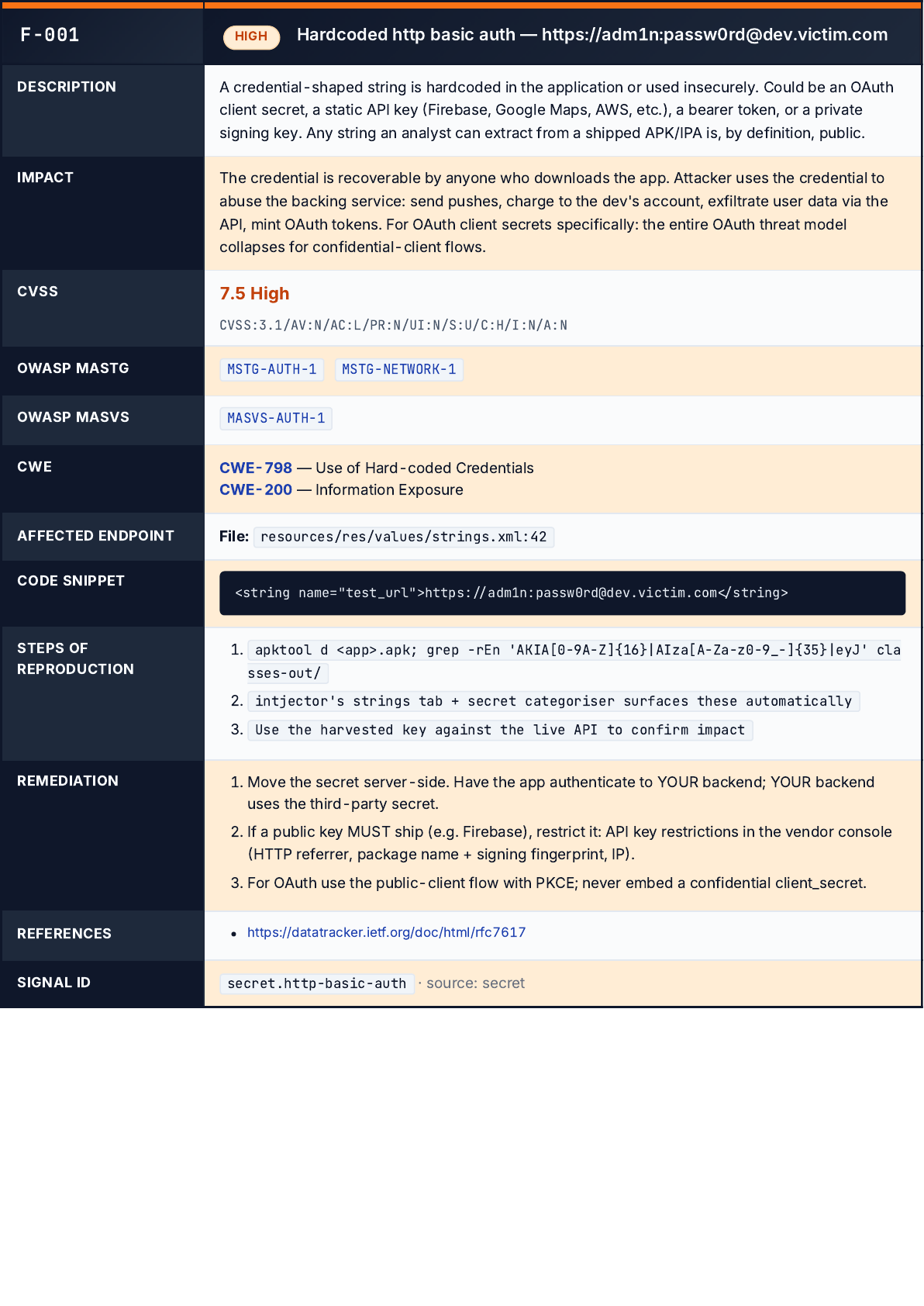
Risk Signals dashboard
Every finding tagged CRITICAL / HIGH / MEDIUM / LOW, filterable by severity + search, mapped to MASTG test IDs. A "detected vs documented" toggle shows which MASTG checks actually fired on this build versus which are just part of the catalog.
MASTG alignment
Each signal links to a specific MASTG test case (MSTG-STORAGE-*, MSTG-CRYPTO-*, MSTG-NETWORK-*, MSTG-PLATFORM-*, MSTG-CODE-*, MSTG-RESILIENCE-*). The output can be used directly in a pentest report.
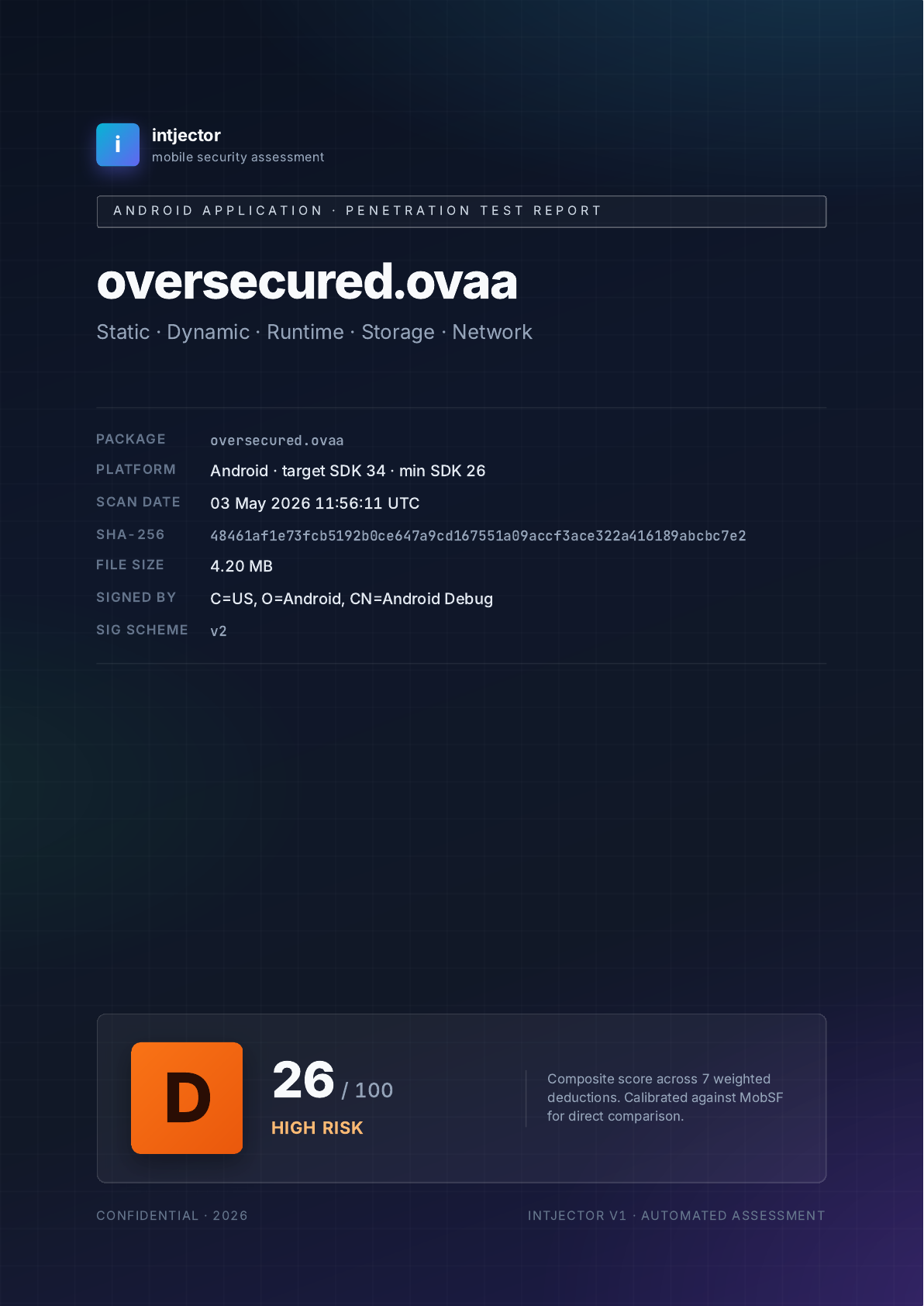
Exportable reports
Export findings as JSON for automation, Markdown for GitHub / Notion, or Excel (.xlsx) for client delivery. The Excel export includes a dedicated MASTG and MASVS checklist sheet with pass / fail / not-applicable status per requirement.
Browser-first UX
Everything runs in a single web UI: upload, scan, attach, patch, report. No terminal, no Frida CLI setup, no Python environment to configure. Share the URL with your team — sessions persist across users.